There isn’t a week that goes by when you don’t read about some data breach. Safeguarding your personal information starts with understanding cybersecurity risks, knowing what to look for, and doing everything you can to help protect yourself.
A growing problem
- Last year, identity theft continued to grow, setting 2024 up as another year of ever-increasing cybersecurity issues. Here are a few statistics:
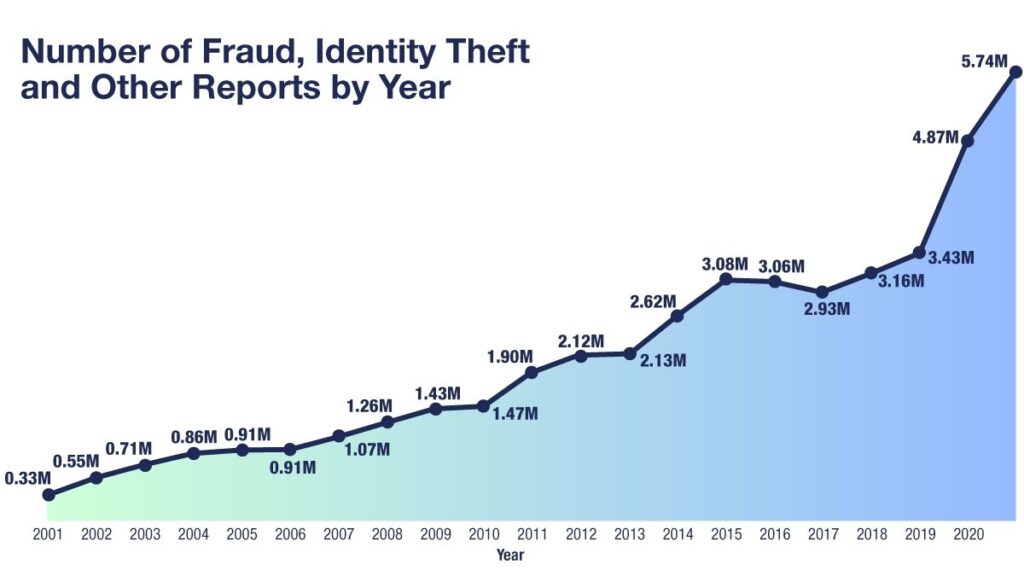
- In 2023, the Federal Trade Commission (FTC) received a total of 5.7 million fraud and identity theft reports.
- Georgia, Maryland, Delaware, Nevada, and Florida were the five states reporting the most identity theft cases per capita. South Dakota had the lowest.
- The median loss for victims of fraud cases is about $500.
- Total losses are estimated to be $10.2 billion.
- Every 22 seconds, identity fraud claims a new victim.
- Nearly 33% of Americans have faced some kind of identity theft attempt.
As the chart below illustrates, the number of reports of identity theft and fraud to the FTC has risen steadily since 2001.1
A growing problem
While businesses, law enforcement, and legislators contend with identity theft, some of the most effective methods to help manage your personal information are in your own hands. There are no-tech, low-tech, and high-tech ways to help address your vulnerabilities.
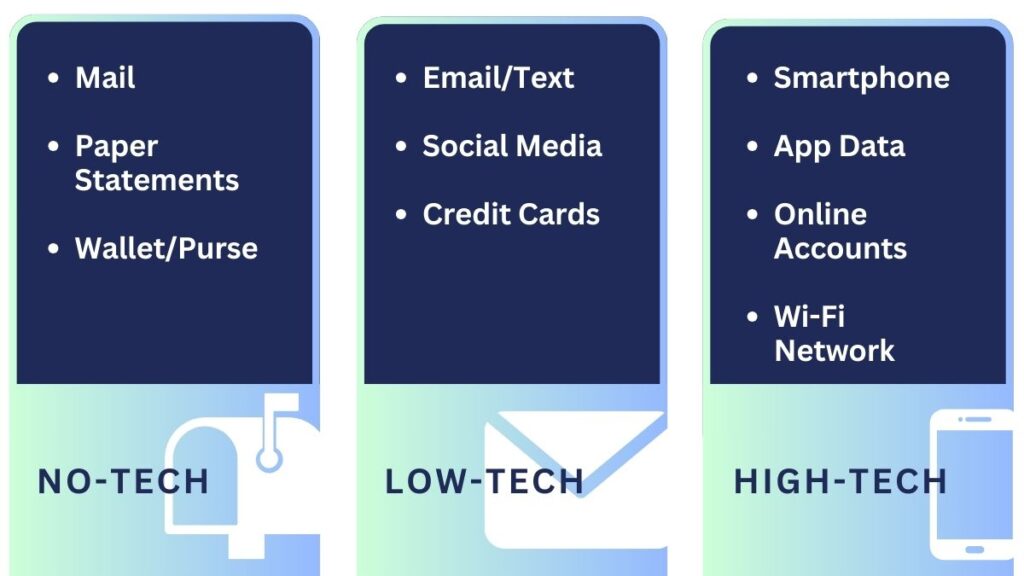
No-tech
You might be surprised to learn that the FTC reports that over half of all identity theft comes from physical documents. You can help manage this risk by taking a few simple actions, such as the following:
- Registering for United States Postal Service Informed Delivery so you know what mail to expect each day
- Buy a shredder and use it for any statements or other documents, including anything that may include any account numbers, etc.
- Go paperless with as many companies as possible.
- Avoid keeping sensitive information in your wallet or purse.
Low-tech
Many “phishing” attacks come from scammers disguised as trustworthy sources. Here are some of the most common types of phishing:2
- Email phishing is the most common, and tactics like phony hyperlinks lure email recipients to share their personal information.
- Malware phishing involves planting malware disguised as a trustworthy attachment in an email. In some cases, opening a malware attachment can harm your system.
- “Vishing” has attackers in fraudulent call centers attempting to trick people into providing sensitive information over the phone.
Here are a few ways to identify some types of phishing attempts:
- Don’t trust email display names—click to see the sender’s full email address. Scammers often create logical display names over their actual addresses.
- Check emails for typos and poor grammar.
- Hover over hyperlinks before clicking.
- Read the salutation; don’t open the email if it looks off.
- Be wary if the email is addressed to “Valued Customer” instead of your name. It’s likely fraudulent.
- Review the signature to ensure the contact information is in the email footer.
- Beware of threats like “Your account has been suspended” via email or phone.
- Be very wary if any sense of urgency is implied or information is requested.
- Be skeptical of any text messages you receive from unknown senders.
High-tech
Some Smartphone apps collect details about you, including age, GPS data, and browsing habits. Make certain you understand if an app accesses your camera, tracks your location, records your audio, or reads your call logs and text messages. Check out the app privacy report occasionally to see which apps are accessing your data. You should be able to turn off data tracking with an app at any time.
Avoid using public phone chargers at airports or restaurants. They can contain malware that gives hackers access to your devices. Use a portable charger instead.
Wi-Fi can be risky, especially in public settings. While at home, you should consider password-protecting your network and keeping router and security software up to date. You might also consider using a virtual private network (VPN) when in public. If you are on a public network, look for sites marked HTTPS. If possible, avoid making financial transactions when using an unfamiliar internet connection.
Peer-to-peer (P2P) Payment Apps like Venmo have become popular for everything from paying babysitters to splitting the check at a restaurant, but they can have some hidden risks. Top P2P scams include:3
- Impersonation scams: Criminals persuade victims to send money by pretending to be someone they’re not, and thanks to artificial intelligence, by which scammers can now clone voices and faces, these scams are becoming even more challenging to detect.
- Fake seller scams: Criminals advertise a phony product or service online, collect your money upfront, and disappear without delivering the goods.
- Advance-fee scams: A scam where someone claims you’ve won a prize and offers to send your winnings in exchange for you sending them a service fee.
- Venmo is owned by PayPal. Remember, any companies mentioned are for illustrative purposes only. It should not be considered a solicitation for the purchase or sale of securities.
To protect yourself from P2P scams, only use these payment apps with people you know and trust, such as friends, family, or local businesses. Consider using a credit card if you’re transacting with someone new or unseen. Credit card providers may offer some level of fraud protection as part of their value proposition.
The best defense is a good offense
You can take proactive steps to defend against identity theft and fraud, such as strong passwords, multi-factor authentication (MFA), and credit monitoring.
Create, manage, and store strong passwords 4
- Consider using a password manager.
- Password managers store and organize your passwords with secure digital encryption and multi-factor authentication.
- Certain password managers are designed to connect your login information across multiple devices, websites, and apps.
- Some browsers have built-in password managers that can help.
- There are many password managers you can subscribe to with a variety of features and benefits. Here are some of the most popular, according to a 2024 report from Cybernews.com.5
- NordPass
- 1Password
- RoboForm
- Keeper
- Bitdefender
.If you are not using a password manager, you should focus on password strength. As a general guideline, strong passwords:
- It should be at least 12 characters long, but 14 or more is better.
- It is a combination of uppercase letters, lowercase letters, numbers, and symbols.
- These are not words found in a dictionary or personal names, characters, products, or organizations.
- Are significantly different from your previous passwords.
- It should be easy for you to remember but difficult for others to guess.
Once you’ve created a strong password, keep it secure:
- Never send a password by email, instant message, or any other means of communication that is not reliably secure.
- Consider using a unique password for each website.
- You can write your passwords down, but keep them in a safe location.
- Change your password immediately if you suspect an account is compromised.
- Get in the habit of changing your passwords periodically.
Use online providers that employ multi-factor authentication (MFA)
If you don’t know the term “multi-factor authentication,” you may have seen it in action. If you’ve ever tried to log into an account and received a text with a code you need to enter, or you are asked a series of questions like “Who is your high school best friend,” or “What was your first car,” you have used multi-factor authentication (MFA).
MFA is an identity verification method in which users must supply at least two pieces of evidence to prove their identities. It may be annoying, but it’s worth it. MFA blocks 99.9% of modern automated cyberattacks.6
Monitor and/or freeze your credit
You can monitor your credit using the three main credit service providers. You can also take the additional step of placing a freeze on your credit. Freezing your credit may help prevent fraud because it prevents new lines of credit from being opened without your permission. The cost is free, but keep in mind that the freeze remains in place until you remove it.
Contact the national credit bureaus to request fraud alerts, security freezes, and opt-outs from prescreened credit offers. Each firm has its own guidelines, so ensure you understand the rules before placing restrictions on your account.
- Equifax – 800-685-1111
- Experian – 888-EXPERIAN (888-397-3742)
- TransUnion – 888-909-8872
While security systems have been put in place by most companies to monitor and fight large-scale cyber threats, it is important that you stay vigilant regarding your own cybersecurity, passwords, and identity. Your day-to-day routines are the first line of defense.
1. IdentityTheft.org, January 2024 https://identitytheft.org/statistics/#:~:text=The%20FTC%20received%205.7%20million%20reports%20of%20identity,fraud%2C%20up%20from%204.7%20million%20the%20previous%20year.
2. Microsoft.com, February 2024 https://www.microsoft.com/en-us/security/business/security-101/what-is-phishing
3. AARP.org, January 2024 https://www.aarp.org/money/scams-fraud/info-2024/safely-send-money-on-zelle.html?intcmp=AE-FRDSC-MOR-R2-POS3
4. Microsoft.com, February 2024 https://support.microsoft.com/en-us/windows/create-and-use-strong-passwords-c5cebb49-8c53-4f5e-2bc4-fe357ca048eb
5. Cybernews.com, February 2024. Any companies mentioned are for illustrative purposes only. It should not be considered a solicitation for the purchase or sale of the securities. Any investment should be consistent with your objectives, timeframe, and risk tolerance. https://us.cybernews.com/lp/best-password-managers-us/?utm_source=bing&utm_medium=cpc&utm_campaign=Bing_CN_PM_S_T1_US_G-B_All-Lang&utm_content=82669896208215&utm_term=best%20password%20manager&utm_id=414415436&campaignId=414415436&adgroupId=1322713715420697&adId=82669896208215&targetId=kwd-82670572028797:loc-4116&device=c&munique=87a532ab2a9f1f6111ef577d5d1ec55e&source=bing&medium=cpc&campaign=Bing_CN_PM_S_T1_US_G-B_All-Lang&content=82669896208215&term=best%20password%20manager&msclkid=87a532ab2a9f1f6111ef577d5d1ec55e
6. Zippia.com, February 2023 https://www.zippia.com/advice/mfa-statistics/
